Splunk SIEM
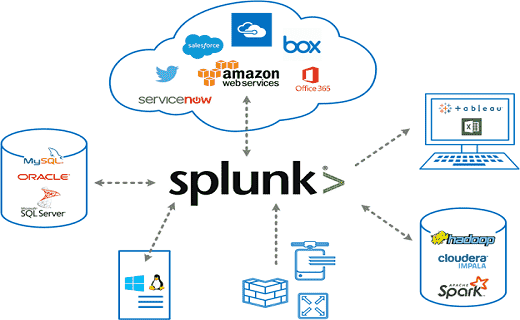
What is Splunk used for? - Splunk is a technology that is used for searching, monitoring, visualizing, and analyzing machine data on a real-time basis. It is a tool for log management and analysis. Most people have a common question: Is Splunk a SIEM? Splunk is not a SIEM but you can use it for similar purposes. It is mainly for log management and stores the real-time data as events in the form of indexers. It helps to visualize data in the form of dashboards.
What Is the Concept of Splunk with SIEM?
Features of SIEM - What is Splunk used for?
Most SIEM cannot keep pace with the sophistication and rate of recent cyber threats. This is an analytically driven security solution that goes beyond SIEM to deal with advanced threat detection, security monitoring, incident management, and forensics on a real-time basis. This analytics-driven system can improve your visibility across multiple systems and with cross-collaboration it provides a strong security system.
Features of Splunk are:
- Visibility: it allows us to collect non-security and security data across organizational silos and multi-cloud environments for better investigations and incident response.
- Efficiency and context: it allows to de-duplicate, collect, aggregate, and prioritize the threat intelligence from different sources improving the security investigations and efficiency as security operations are streamlined.
- Flexibility: it is a modern platform of big data that allows you to solve and scale security use cases for your security operations center, compliance, and security operations. It is quite flexible and can be deployed on the cloud, on-premises, or hybrid environment.
- Behavioral analytics: by making use of machine learning detected issues you can optimize the security operations and speed up the investigation, reduce complexity, and respond to attacks and threats faster.
Why should you replace traditional SIEM with Splunk?
Limitations of Traditional SIEM:
- Limited security data types
- Inability to ingest data effectively.
- Slow investigation system
- Not offering scalability and unstable system
- Quite slow and uncertain roadmap.
- Closed ecosystem
- Limited to on-premises deployment.
- Use cases are not actionable.
Benefits of Splunk:
- Enhanced GUI with dashboards
- Faster troubleshooting with instant results
- Best suited for root cause analysis
- Get access to create dashboards, graphs, and alerts
- Investigate and search for specific results
- Monitor business metrics for informed decision making
- It is artificial intelligence coupled with traditional SIEM as a Service.
- Better log management from multiple sources
- Accepts data in multiple formats
- Can create one central repository for Splunk data collected from multiple sources
Products of Splunk:
Splunk Enterprise Security:
it is a SIEM system that makes use of machine-generated data to get operational insights into threats, vulnerabilities, security technologies, and identity information.Splunk Enterprise:
it is a system that collects and then analyses the big data which is generated by the systems, technology infrastructure, and apps to get complete visibility across the security stack of your business.Splunk Adaptive Response:
it is the framework for adaptive operations and in this, the top most security vendors collaborate to improve security operations and strategies for cyber defense.
The architecture of Splunk:
Splunk architecture consists of the following components:
- Universal Forward: it is a component that is lightweight and pushes log data into Splunk forwarder which is heavy. It is installed on the application server or client-side.
- Load balancer: it is the default load balancer of Splunk but you can couple it with your load balancer too.
- Heavy forward: this is the heavy component that allows you to filter the data i.e. you can collect only error logs or so.
- Indexer: this is used to store as well as index data to improve the search performance of Splunk.
- Search head: it is performing the role of performing reporting and helps to gain intelligence.
- Deployment server: it is used to deploy the configuration.
- License manager: it checks the licensing details of the user. The licensing is done based on usage and volume.
Best practices for using Splunk:
- Make sure to test the index so that the test can be performed quickly.
- It is important to get specific fields right at index time. Other things can be created or modified after indexing.
- In Splunk, there is a feature of automatic event breaking. So make sure that the start and end of the event are properly detected by Splunk.
- The timestamp is automatically detected by Splunk. If you are using a different timestamp then configure it before using it.
For more information about Splunk and SIEM tools do contact us https://www.comodo.com/partners/mssp/. We can provide you with the best assistance about SIEM tools and their setup. To know what is Splunk SIEM used for? Reach our experts.
Related Resource