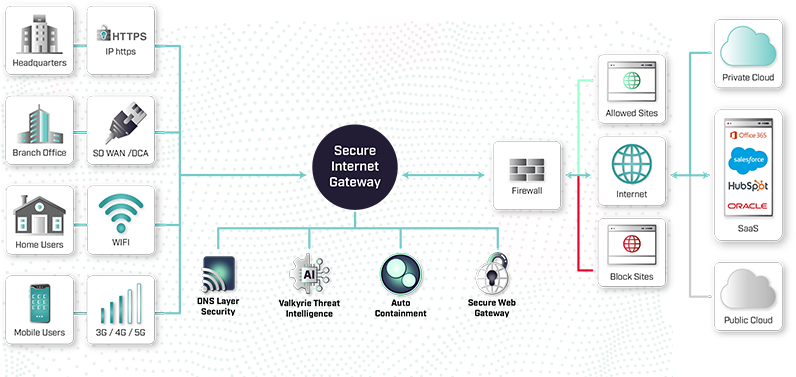
Secure Internet Gateway
Protect against web threats and regulate web browsing activities for your users on any device, in any location, and access to full visibility.
Control Secure Online Browsing Using Secure Internet Gateway
- Ensure Safe Internet Usage
- Quick Setup, Easy to Customize
- Protect Against Online Threats
- Threat Intelligence Integrations
Prevent Unsafe Internet
Browsing
There are links to malicious websites everywhere and hackers are using sophisticated tactics to lure users into clicking them. Employees are smart, but they’re not all cybersecurity experts. Whether your employees are remote, mobile, or in the office, corporate web browsing rules can be applied and monitored.

Customize and Control Internet Usage.
In under two minutes, you can deploy Secure Internet Gateway and protect your network against internet-based threats, while simultaneously preventing unproductive web browsing. Add your network, confirm the recommended security policy and change your DNS settings.
Complete 100% Internet Threat Prevention
Protect all employee devices including desktops, laptops, tablets, and mobile.
Protect all employees regardless of where they are, including remote and mobile employees. Gain visibility of all device web traffic in real-time for safer, more productive web browsing. Comodo Secure Internet Gateway is a cloud-based web filtering solution delivered at the DNS layer, serving as your strong first layer of defense.

Get Deep Insights into the Dark Web
Receive highly refined internal & external threat intelligence feeds to alert or block on Indicators of Compromise. Incorporate your companies own internal intelligence into Comodo’s Dragon Enterprise for added coverage. Complete Valkyrie integration for checks on process execution via MD5 hash submission.
Blacklist or Whitelist Domains
80+ content categories updated with millions of new domains every 2 hours, plus custom blacklists and whitelists.
Set Custom Protection Policies
Protect against 100% of unknown online threats per company, location, endpoint, mobile device, IP, subnet and user.
Advanced Web Threat Protection
Block phishing, malware domains, malicious sites, botnets, C&C callback events, and web-borne attacks.
Customizable Blocked Webpages
Add your logo, add a message and show different pages for each category to inform employees why webpages are blocked.
Cloud-Based Architecture
Our lightweight agent sends updates automatically through the cloud to ensure the latest threats are always blocked.
Deploy Instantly with Anycast DNS
No need to install an agent onto your endpoints or network. Get protection immediately over Anycast DNS.
Valkyrie Verdicting Engine
Conducts multiple arrays of run-time behavioral analysis against unknown files to provide a verdict of safe quickly and automatically or malicious.
Auto Containment Ready
Automatically runs from patented virtual container that does allow threats to access the host system’s resources or user data.
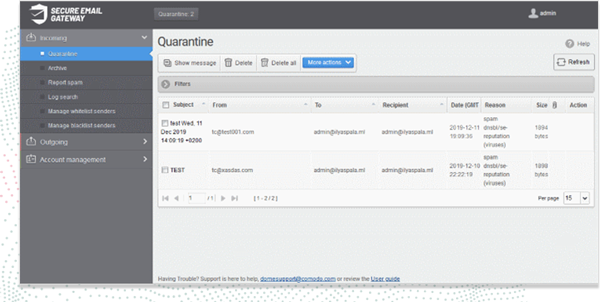
Reporting & Documentation
Every threat found in your environment will be reviewed, transcribed and shared with your regularly created tailored reports.