Secure Email Gateway
Email security to protect your remote and onsite workforce from email phishing threats and email spam.
Prevent Malicious Emails to your Inbox Using Secure Email Gateway
- Keep Malicious Emails Out
- Quick Setup, Easy to Customize
- Protect Sensitive Business Data
- Threat Intelligence Integrations
Protect your network and users.
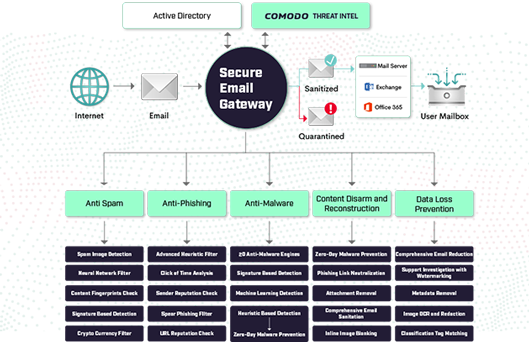
Malicious emails are everywhere and pose as legitimate communication from coworkers and connections, luring users to click. With Zero Trust architecture, businesses can prevent damage from malicious emails. Comodo’s Secure Email Gateway never trusts and always verifies 100% of unknown files, providing businesses with bulletproof email security and an uninterrupted user experience.

Centralize, Customize, and Control Inboxes.
Quick and easy deployment, customizable policies, advanced search options and compatibility with all major MTAs. Security needs differ from employee to employee. Apply security profiles and permissions for various departments and users to protect sensitive data within the organization. Automatic cloud delivered updates keep you up to date.
Complete 100% Threat Prevention.
Our Secure Email Gateway system uses a sophisticated array of spam filters, anti-virus scanners, and content analysis engines to keep spam out while letting legitimate communications in. Even if an unknown gets to a user inbox, the threat is already inside Quarantine while our patented auto containment eliminates the threat’s runtime from executing its malicious payloads.

Get Deep Insights into the Dark Web
Receive highly refined internal & external threat intelligence feeds to alert or block on Indicators of Compromise. Incorporate your companies own internal intelligence into Comodo’s Dragon Enterprise for added coverage. Complete Valkyrie integration for checks on process execution via MD5 hash submission.
Anti-Spam Email Protection
Sophisticated array of spam filters, anti-virus scanners, and content analysis engines to keep spam out and emails in.
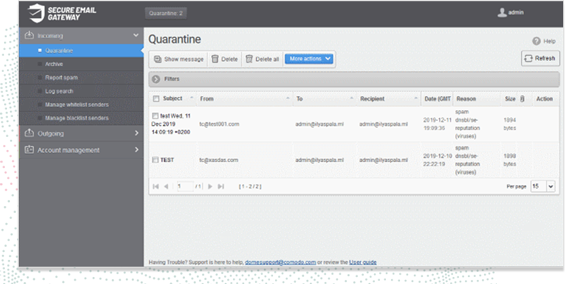
Quarantine Malicious Emails
Protect against 100% of unknown email threats, without user interruption. Block spam before it even enters the network.
Spear Phishing Email Security
Prevent email-spoofing and bad actors, impostors that target your organization’s sensitive information through user error.
Simple LDAP and AD Integration
Integrate your current Lightweight Directory Access Protocol or Active Directory configurations seamlessly.
Cloud-Based Architecture
Our lightweight agent sends updates automatically through the cloud to ensure the latest threats are always blocked.
Email Audit Logs and Data Backups
Easily access any emails in the archive,
without losing any past emails. Perform searches to locate information quickly.
Valkyrie Verdicting Engine
Conducts multiple arrays of run-time behavioral analysis against unknown files to provide a verdict of safe quickly and automatically or malicious.
Auto Containment Ready
Automatically runs from patented virtual container that does allow threats to access the host system’s resources or user data.
Reporting & Documentation
Every threat found in your environment will be reviewed, transcribed and shared with your regularly created tailored reports.