Guided Onboarding and Deployment Advisory Professional Services
The key to ongoing success is implementation to fit your IT infrastructure, resource availability, experience, operational practices and corporate goals tied to your tailored end to end security solution.

Get Started on Dragon
Platform with Success Professional Services
- Frequent Ticket Resolutions
- Regular Health Checks
- Be Comodo Confident on Dragon
- Security Posture Configured to you
- Maximize your Investment Returns

Your trusted contact for ticket handling
Take the uncertainty out of maintenance notifications and prompts. Technical Account Management will provide your IT staff proactive communication on maintanence and outages. Be certain specific tuning and advanced configurations for any complex or simple environment gives you full control and visibility towards Active Breach Protection.

Keep all technologies running smoothly
Stop questioning whether or not an upcoming update will breakdown your installation. Technical Account Management will keep open communication about the updates, upgrades and feature enhancements you plan on deploying. We will work closely with your internal IT staff to accommodate any changes based on best practices

Reduce Complexity, Gain Results
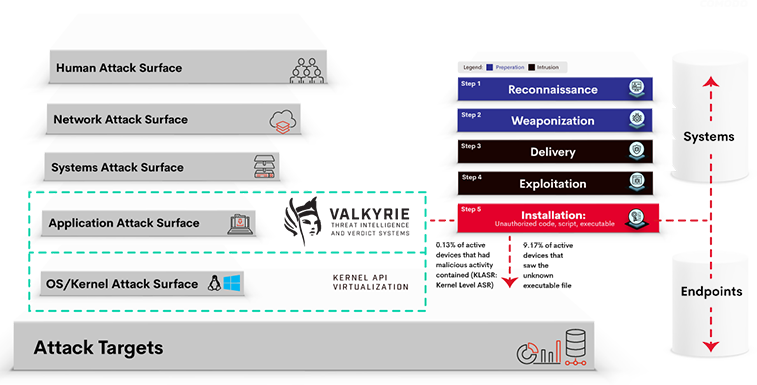
Be certain specific tuning and advanced configurations for any complex or simple environment gives you full control and visibility towards Active Breach Protection. Your staff will learn from our knowledge transfer process to assure successful ongoing operations and administration. Get your IT staff ready for major updates to ensure uptime and day to day operations are running smoothly.
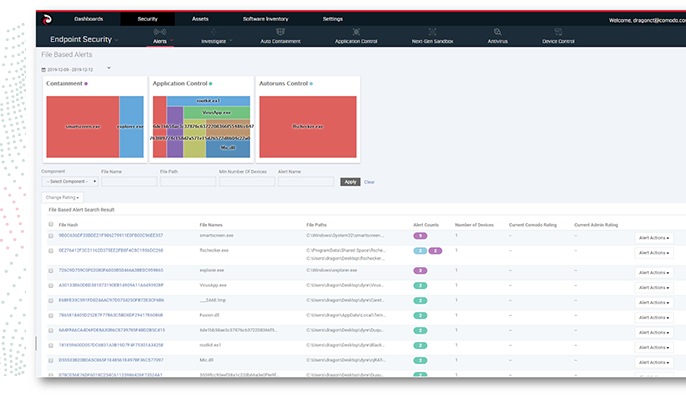
Verify Every Loose Endpoint
Our customer success engineers are completely 100% dedicated to fine tuning your endpoint security to work best with your current infrastructure and environment setups. We will work to understand your business and security requirements to ensure Dragon Platform isaligned for your success in preventing malicious threats from affecting your operations and business continuity.
Breaches aren’t cheap. We keep you secure.
No one can stop zero-day malware from entering your network, but Comodo can prevent it from causing any damage. Zero infection. Zero damage. Current security solutions depend upon detection before they can prevent. Detection efficacy rates are not good enough.
Setup Configuration & Deployment
Guided setup configurations adhered to the strategic plans to best suite your environment for high investment returns.
Security Performance & Optimization
Protect against 100% of known, unknown threats with precisely configured and maintained Auto Containment.
Dedicated Ticket Handling
Your dedicated TAM will regularly facilitate and provide expert guidance on resolving potential issues and resolve tasks.
Training & Knowledge Transfer
Your internal IT staff will be trained to handle any upcoming update to prevent interruptions on your security installation.
Custom Guided Deployment
Guided setup configurations adhered to the strategic plans to best suite your environment for high investment returns.
Reporting & Documentation
Actionable information based on your data
will deliver customized reporting related to your own environment’s logs.