What Is the SIEM Process and Strategies?
Cybersecurity is transforming each passing day leading to a high rate of security threats. Most organizations are putting in place prevention measures to detect threats caused by the modernized cybersecurity efforts. Siem, security analysis, and artificial threat intelligence is on the verge of providing essential capabilities to facilitate and detect threats. The siem server is referred to as a log data management platform. Which involves collecting data and managing it facilitating analysis and retention of historical data. Siem is more of a product. An organization needs to follow a particular Siem Process to optimize threat detection and easily protect one's network. Here is a brief discussion on the process that your organization needs to follow.
1. Proper Deployment
If your organization is thinking of deploying a Siem security system as a threat detector then there are a couple of questions that need to be answered before installing the siem solution. For instance, some of the questions include;
- Where exactly will the deployment of the Siem solution be done? Which database, digital asset and network areas will need monitoring and detection of threats? Is your organization fully aware of its network extent?
- As an Enterprise is your team thinking of deploying difference between Managed SOC and siem and security analytics at the same time? Is the deployment done location by location or cautiously?
- As an organization is your team of professionals ready to monitor and take care of the installed siem solution? The Siem solution needs unending attention and scrutiny to function appropriately.
- You should know the security issues you are deploying the Siem solution to deal with.
Once you figure out as an organization the answers to the above questions, you will be able to know the right siem solution to deploy in your organization.
2. Data Collection
Siem solution collects log data and events from numerous enterprise systems. Each device initiates an event in real-time especially when anything happens and later on, events are collected which are further stored on a database. Siem solution collects data in four different ways;
- Through an agent that has been installed on the machine.
- By connecting instantly to the gadget either through an API call or a network treaty.
- By obtaining log files instantly from storage by using Syslog format.
- Through event streaming protocols such as; Netflow or IPFIX.
Siem security solution is obligated to the collection of data from different devices, systematizing it, and further saving it in a design that will enable easy analysis.
3. Data Management
Organizations that store data in large amounts need to consider the following Siem Process when installing siem solutions.
- Storage should be done either on-premises or the cloud or one might consider merging the two.
- Optimization and indexing to enable productive analysis and survey.
- Tiered. This involves hot and cold data. Hot data which is normally used for real-time security monitoring should be stored in high performance while cold data that your organization may want to scrutinize one day should be stored on high volume storage that’s inexpensive.
4. Log Retention
Industry standards such as;
- PCI DSS.
- HIPAA.
- SOX.
They need log data and events to be kept for about one to seven years. Large organizations create huge tons of log data each day from their IT systems. Siems needs to ensure that it chooses wisely what to retain for either compliance or forensics requirements. Some of the strategies siem uses to reduce vast log volumes include;
- Syslog servers - It is a normal server that standardizes data logs, storing only vital information in a regulated format. Syslog servers enable organizations to compress log data and retain vast amounts of historical data.
- Deletion schedules - Siem automatically gets rid of old logs which are of no use for compliance. This is made possible by accessing log data files instantly with the help of Syslog servers from storage.
- Log Filtering - Not every data log is needed to suit the compliance requirement facing your organization. Data logs can be filtered by set rules, source systems, or times created by the Siem director.
- Summarization - Log data can be optimized to maintain only vital data logs elements for instance events and unique IPs.
5. Requires Human Intervention
Your security team of professionals needs to be actively involved in this entire process. Your whole entire organization needs to be trained also on the whole process. Through this, they will also be able to detect any digital malicious activities and report them directly to your security team. The Siem Process needs constant monitoring which cannot be only provided by your team of security.
Summary
The above-discussed procedure is the Siem Process that can be followed vividly by organizations when installing siem solutions that will in turn detect security threats.
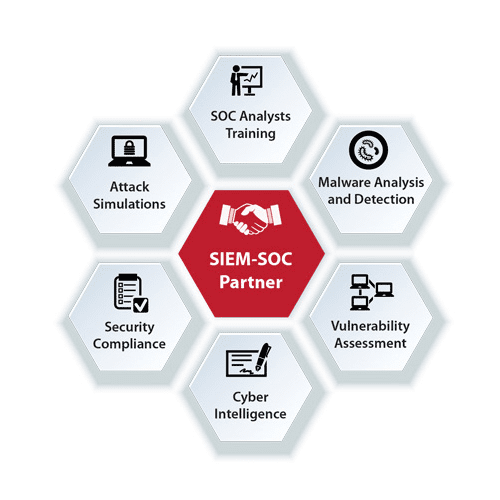
Difference Between SOC and SIEM
Related Resource