Security Operation Center Definition
In a world of digitalization, digital products have become an integral part of people's lives. The rapid growth of digitalization in the business environment unavoidably has become a magnet for public attention. With the increased use of the internet, every business firm uses the internet as a medium to reach its audience. And the internet world is never free from hackers. One of the biggest challenges that come in the way of a business firm is how to conduct online activities smoothly. How to keep their computer network secure from hacks? Also, speedy cloud adoption has its own set of risks and complexity of security obstacles.
What is SOC in Cyber Security?
Hackers constantly develop new ways to inroads to the computer network and access the important data. These data can be used for various illegal activities. This will lower the secrecy of the business organization. More than fifty percent of business firms around the globe deal with cyber-attacks.
Thus, it becomes important to protect data and nullify threats to their business. The soc network is an optimal cyber-security strategy to eradicate the problems faced by a firm.
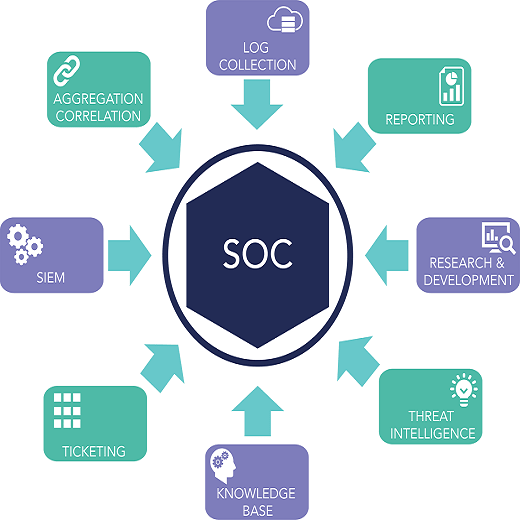
Security Operation Center (SOC) Network
A security operation center network is a centralized unit that allows a business to coordinate and achieve cyber-security. At a SOC, there is a team of experts who develops and enforces security policies. They implement the necessary technology to keep a check on recognized threats to a network.
Member of Security Operation Center (SOC) team
A Security Operations Center is a team of experts that has cyber-security personnel, security analysts, and engineers. They work together to combat cyber attackers.
The members of the SOC team are-
A SOC manager
- Tier 1 Alert Analysts
- Tier 2 Incident Responders
- Tier 3 Subject Matter Experts (SMEs)
The need for a SOC as a Service (Security Operation Center)
Every organization is needed to have a team to fight against hackers. This will show significant growth in business affairs. The benefits of having a security operation center are as follows-
- Centralized Approach
The SOC team takes a lead when there is any breach or threat. The SOC as a Service team continuously keeps an eye on the entire network and any threat to the firm. They share the necessary information with the entire team members. This helps them to identify and counteract threats. - Cost control
The entire SOC team is located in one place. They monitor the activities of the business from a single location. This reduces the cost of hiring specialists who will be scattered at different locations. The firm needs to bear the cost of multiple rooms and other expenses. This will increase the recurring expenditure of a business. - Continuous proactive monitoring
The SOC team uses techniques that scan the network continuously. They keep a check on suspicious activities so that they can be detected at the earliest. Continuous check on the network allows the team to mitigate such threats. The advanced monitoring tools reduce the task of humans. - Log management
The SOC team is responsible for multi-task. They collect, maintain, and review the log of all network activity of an organization. They try to find a connection between those data collected from applications, firewalls, and operating systems. They identify the existing threats and can use remedies for such threats.
How to get the best result of Security Operation Center team
- SOC teams should update themselves with the latest technologies and bits of intelligence to enhance their detection and security capacity.
- SOC as a service acquires data from the firm. They try to tie in the information from external sources. The team tries to correlate and understand the threats.
- They use security automation to work effectively and efficiently. By aggregating high-skilled experts and security automation firms will enhance their analytical power to defend against cyber attackers
There is a popular proverb. “Prevention is better than cure”. No matter how much cost you need to bear, your firm should have a SOC team. Every day we hear about cyber-attack in the security network. Such an attack on a firm's network, results in losses of its data and many of its secrets files. These attacks lead to huge financial losses and sudden unexpected costs to the firm. Such threats can injure your firm.
SOC Cyber Security
To uplift your organization's function, you need to make a choice. Either you can have an internal SOC team or use a third party to outsource a SOC. Having a SOC team will bring more transparency to your organization. Your expert panel will provide continuous service. They will monitor the threats. To fight against cyber-attackers, a firm should have a good security operation center team.