ARE THREATS LURKING ON YOUR ENDPOINT?
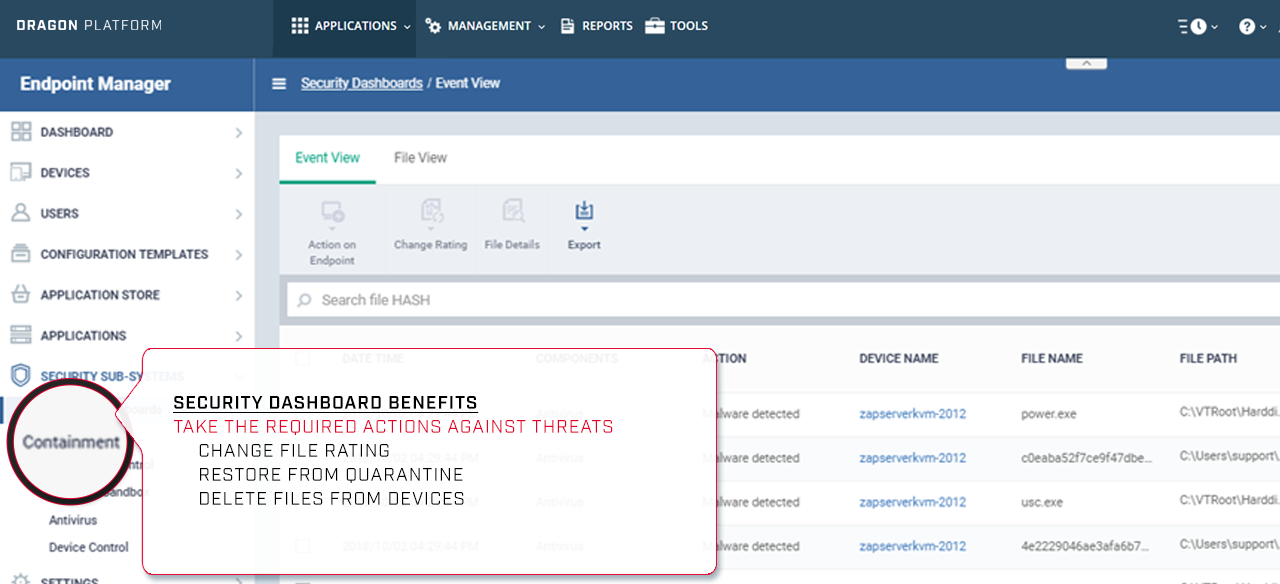
Quickly identify if malicious or unknown files reside on your endpoint
secure endpoints with a ZERO TRUST architecture
Advanced Endpoint Protection will never trust and will always verify 100% of unknown executables
endpoints finally protected
It is mathematically impossible to stop 100% of cyber threats from entering your network. Advanced Endpoint Protection bulletproofs endpoints by restricting threats of their write privilege to the hard drive, CPU and registry. Only Comodo AEP provides trusted verdicts on every unknown file 100% of the time.
VIEW SOLUTION BRIEF
Protect endpoints against 100% of unknown threats, without impacting user productivity.
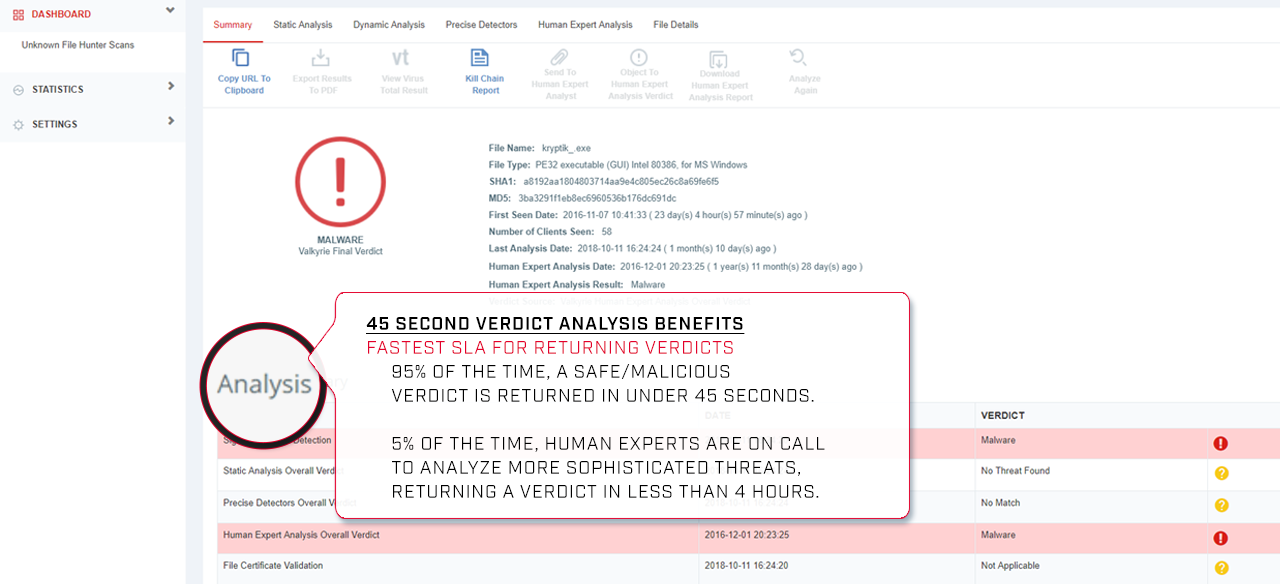
Combination of machine learning and human expert analysis returns verdicts in under 45 seconds.
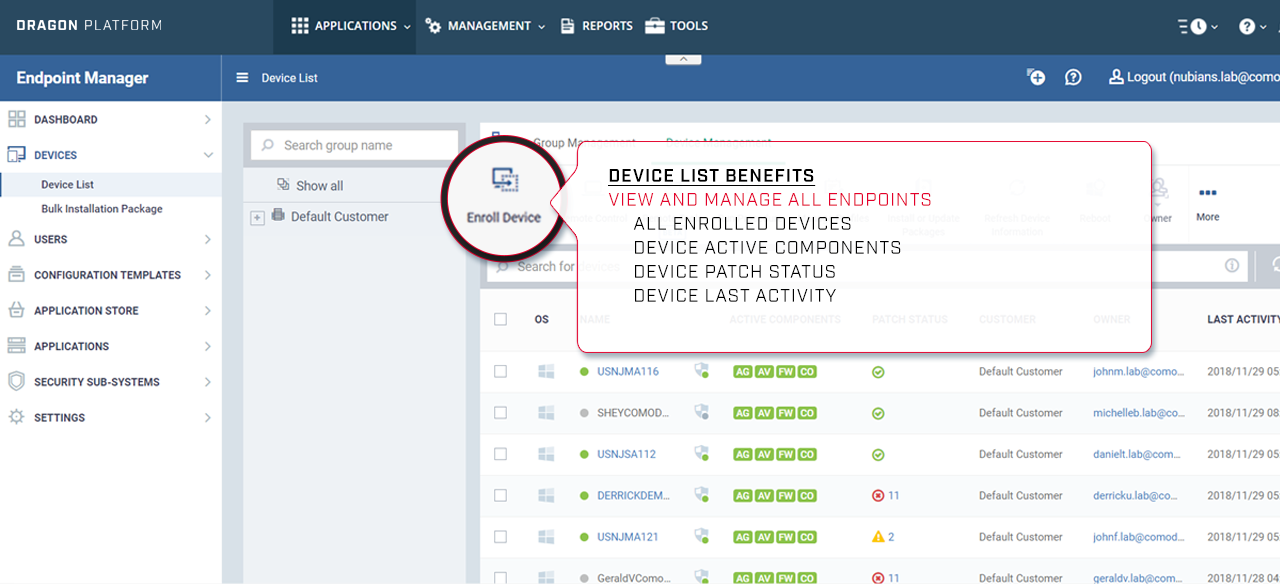
AEP is managed within a centralized platform with real-time visibility and a lightweight client.

OUTSMART CYBER THREATS
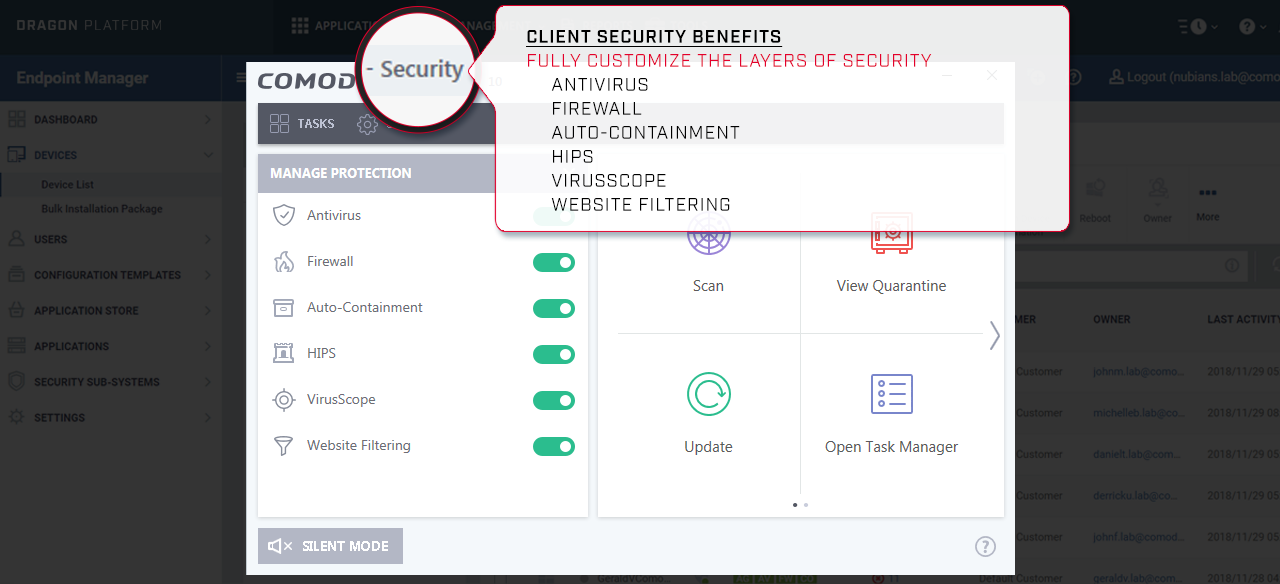
Comodo Cybersecurity AEP utilizes Comodo's patented Auto-Containment Technology to prevent zero-day threats like no other vendor in the market. When an unknown file, a potential malicious threat, attempts to execute on an endpoint, the file is immediately encapsulated by Comodo Containment Technology, while users can immediately open files and run downloaded scripts and executables.
- Allow unknown files to safely run on endpoints, without write privilege to critical system resources.
- Virtualize all unknown files immediately in Auto-Containment when executed on an endpoint.
- End users enjoy seamless productivity, with the ability to immediately run
any unknown file, even while the file is in analysis.
ALL UNKNOWNS BECOME CLASSIFIED
While unknown files are in containment, the files are immediately analyzed in the cloud by Comodo's Valkyrie Verdicting Engine.
- 95% of unknown files return a verdict in under 45 seconds!
5% are sent to human security experts with a 4 hour SLA! - Security experts are on call 24/7, analyzing more sophisticated
threats, returning a verdict in less than 4 hours. - All file verdicts are updated globally in real-time for all AEP
customers by the Valkyrie Verdicting Engine.

Advanced Endpoint Protection
Prevent 100% of unknown files from damaging your endpoints, with an uninterrupted user experience
Contain 100% of unknown threats instantly
Automatically detect, cleanse and quarantine suspicious files
Protect against inbound threats and outbound threats
Check the file reputation against Comodo's whitelist and blacklist
Monitor behaviors of all processes to identify harmful actions
Monitor important OS activities for intrusions
Protect against threats that are not files
Statically and dynamically analyze unknown threats in the cloud
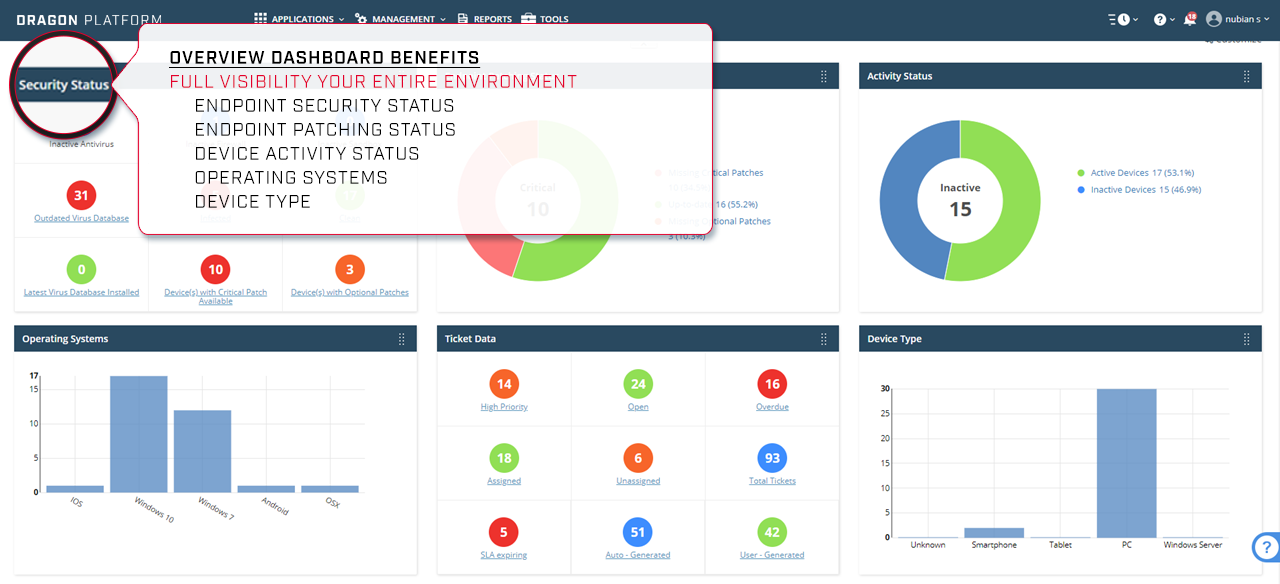
Centralized overview dashboard of endpoint activity
24/7/365 expert analysis of more sophisticated threats
Contain 100% of unknown threats instantly
Automatically detect, cleanse and quarantine suspicious files
Protect against inbound threats and outbound threats
Check the file reputation against Comodo's whitelist and blacklist
Monitor behaviors of all processes to identify harmful actions
Monitor important OS activities for intrusions
Protect against threats that are not files
Statically and dynamically analyze unknown threats in the cloud
Centralized overview dashboard of endpoint activity
24/7/365 expert analysis of more sophisticated threats
add-on modules
Endpoint Detection & Response
Pair Endpoint Detection & Response with Advanced Endpoint Protection for increased endpoint visibility to detect threats and investigate and respond to security incidents.
LEARN MOREManaged Detection & Response
Pair Managed Detection & Response with Advanced Endpoint Protection to outsource the management of your networks and endpoints to Comodo to prevent breaches.
LEARN MORE- Analyst Recognition





We've won consecutively across many verticals with our premier technology. Innovation happens only when this type of dedication to cybersecurity reaches the many.
Comodo Named to Gartner Endpoint Protection Platform (EPP) Magic Quadrant
Comodo AEP Awarded Silver in Endpoint Detection and Response in 2019 Cybersecurity Excellence Awards
Comodo AEP Named Best in Ransomware Protection in 2018 Cybersecurity Excellence Awards
detection & response
Comodo MDR Named Best in Managed Detection and Response in 2019 Cybersecurity Excellence Awards