A Deep Insight into Assess Vulnerability
Based on the current threat environment, it’s not a perfect idea to conduct assessment vulnerability regularly but it’s a fundamental requirement for any company that wants to protect vital data ensuring that it’s networks and IT systems are not exposed to malicious activities from cyberattacks. If this is not done then your organization is at risk from being attacked. Assessment vulnerability simply refers to the process of interpreting, identifying, categorizing and prioritizing of vulnerabilities found in your computer systems, network infrastructures, hardware, and applications providing the company undertaking the assessment with vital knowledge, risk background, and perception to deeply understand and comprehend the threats to the organization’s requirements and act appropriately.
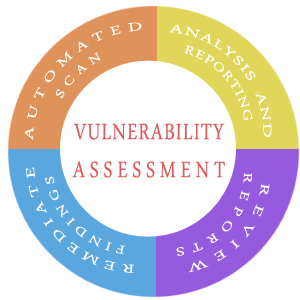
The information collected by the IT security team through vulnerability testing can be controlled by the IT security team to enhance and assess your organization’s threat mitigation and process prevention. In the long-run, Vulnerability assessment helps your organization convey from a receptive cybersecurity approach to a dynamic one. With enhanced awareness of cyber-attacks, your company faces, vulnerability assessment has the ability to prioritize the most important flaws that do need urgent attention. This process is aimed at identifying malicious activities and the risks they bring to the table with the help of automated testing tools for example; Network Security Scanners. The results are further posted on the Assess Vulnerability Report.
Companies from different sizes or an individual who is at risk of experiencing cyberattacks can definitely benefit from vulnerability assessment but very large organizations that produce a huge ton of log data every day are easily subjected to attacks and the use of vulnerability analysis will be of benefit to them. Security vulnerabilities can give hackers access to systems and applications and thus it’s important for the organization to remediate and recognize any weaknesses before any exploitation is done. A combination of in-depth vulnerability assessment and a management program will help organizations enhance their security systems.
Assess vulnerability Benefits.
With this assessment, an organization is provided with detailed information on the security weakness within its environment. Furthermore, it’s able to provide directions on how to deal with the risks that come with those weaknesses and emerging threats. This process offers enterprises with a better comprehension of its security flaws, assets, and risks, in general, reducing the chances of a cybercriminal from breaching your systems off-guard. Administering vulnerability assessment regularly will enable you to get a step ahead of the cybercriminals, identifying holes within your security defenses instead of waiting for a breach to expose them. As an organization plugging holes within your security system will be much easier before cybercriminals discover them.
Vulnerability assessment does not just assess the gaps that might be within your security defense or how easily your network can be breached but it portrays a picture of how your security view might look like for instance; it identifies the vulnerable data helping you prioritize risks that will require immediate attention.
Assess vulnerability might also provide you with more detailed and pragmatic information. With a combination of Breach and Attack Simulation, this tool will automatically process simulated attacks found on your security systems to examine your security view. These two can work perfectly well to improve your entire organization’s security.
Different Types of Assess vulnerability.
Vulnerability Assessment depends on identifying different kinds of systems and network vulnerabilities. This means that the assessment process comprises the use of scanners, different tools, and methodologies to discover vulnerabilities, breaches, and risks. The vulnerability assessment scans include; -
Network-based Scans.
These scans are used to pinpoint any viable network security breaches. This scan can also identify vulnerable systems that are either wired or wireless on networks.
Host-based Scans.
These scans locate or detect vulnerabilities in workstations, other types of network hosts, and servers. Host-based scans usually scrutinized ports and the types of services that are easily noticeable to network-based scans. It also offers perfect visibility when it comes to the configuration of settings and patching of the scanned system history.
Wireless Networks Scans.
With the help of wifi networks, the wireless network scans prioritize on points that can be way attacked by wireless network systems. Apart from identifying wretched access points, this scan can also authenticate an organization’s network if it has been securely configured.
Application Scans.
These scans can be used to evaluate websites to identify any familiar software vulnerabilities and illogical configurations that might be found in network or website applications.
Database scans.
This scan can be used to recognize any weak points found in a database in order to prevent any attacks for instance; - SQL Injection Attacks.
Summary.
A detailed Assess Vulnerability program provides enterprises with in-depth comprehension, awareness, and risk environment necessary to acknowledge threats within their security systems and take measures accordingly
Related Resources: