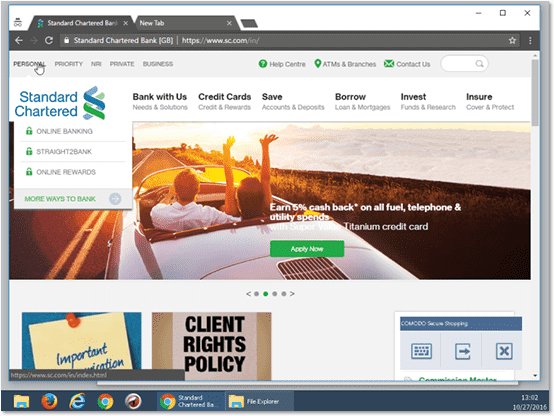
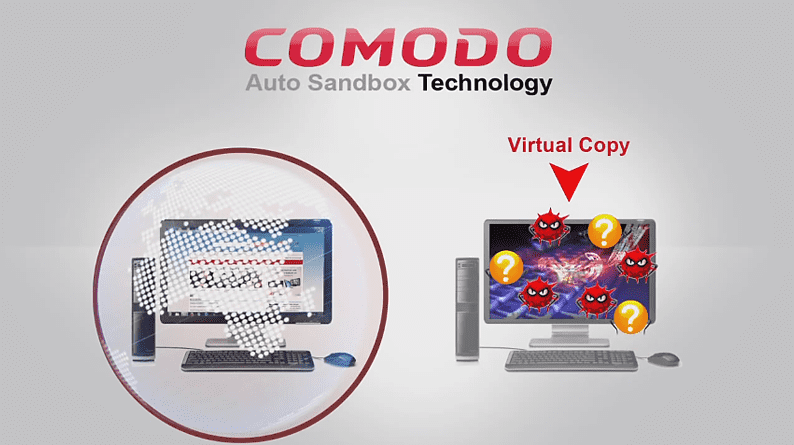
Comodo Complete Antivirus with Complete Internet Security
The complete internet security product with all of our premium features!
Protect your PC from viruses, malware, and hackers.
our best offer ever! $29.99 for a year of protectıon!
Got more than 1 PC? Get 3 Licenses for $39.99

Now Only
$29.99
Per Year!

"Enterprise-Grade
Security For Home"
Security For Home"