Next Generation Endpoint Security with Integrated System Hardware and Software management and Instant User Assistance. Comodo ESM Checks All the Boxes…
Whether deployed as a complete security suite or by using the sandbox as a standalone to fortify existing AV solutions, Comodo ESM offers unrivalled endpoint protection for Microsoft Windows servers, desktops, laptops and tablets.
The full Comodo Endpoint Security suite brings 5 layers of defense (Antivirus, Firewall, Host Intrusion Prevention, Auto-Sandbox & File Reputation) to the point of impact - the desktop environment. Its ground-breaking auto-sandbox technology eliminates malware outbreaks and operating system contamination by automatically running untrusted processes in an isolated environment. This makes Comodo's endpoint protection the only managed anti-malware solution that can offer a $5,000* limited warranty against infection.
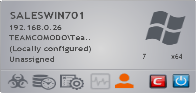
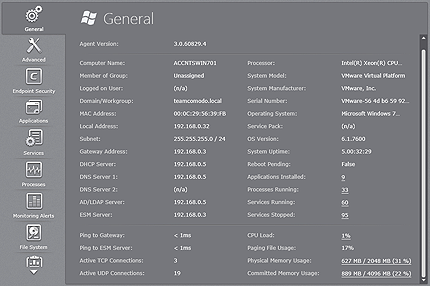
The Comodo ESM dashboard gives administrators panoramic insight and control over all aspects of endpoint protection and management. Its streamlined interface displays 14 critical metrics about each machine, facilitating rapid alerting and remediation of issues. Administrators can also terminate endpoint processes, stop or start services, uninstall applications and delete unwanted files - all without causing interference to the end-user.
Comodo Advanced Endpoint Protection allows you to control and centrally manage endpoint protection through the application of operational templates or policies. Any deviation from these policies causes Comodo ESM to automatically reapply the assigned policy or alert the administrator if it is unable to do so.
Comodo's endpoint protection also provides administrators with the ability to centrally manage endpoint system resources. Administrators can define operational thresholds for CPU usage, RAM usage, network usage and available storage. Should the thresholds be exceeded, Comodo ESM will alert the administrator through the dashboard and via email notification.
Additional policy configurations include power management such as screen-locking or drive-locking. Your Green initiatives are further enhanced through system-standby and system-hibernation scheduling. Comodo's endpoint protection also offers options for disabling USB mass-storage devices, optical devices and even floppy drives.
- technology prevents zero-day malware attacks
- Manages Comodo Endpoint Security, the award winning defense in depth suite built on Comodo’s Default Deny architecture
- Standalone sandbox complements and enhances existing AV solutions
- 'First Glance' of security, system and user issues
- of managed endpoints operation through a single click
- Remote assistance capabilities using SSL encrypted screen-sharing tunnels to LAN and WAN endpoints


Microsoft and Windows are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries.
Apple, Mac and OS X are trademarks of Apple Inc., registered in the U.S. and other countries.
Comodo's endpoint protection is not affiliated with Debian. Debian is a registered trademark owned by Software in the Public Interest, Inc.
Linux® is the registered trademark of Linus Torvalds in the U.S. and other countries.
1 Terms and conditions apply.
Features & FAQ
Features
Centrally managed security for Windows®, Apple® Mac OS X® and Linux® * based endpoints
Automatic Threat containment – Prevents malware outbreaks by detecting then automatically containing untrusted files in an isolated environment separate from the underlying operating system and user data
Multi-layered endpoint defense – Each endpoint is protected with a powerful combination of antivirus, firewall, host intrusion prevention, URL filtering, behavior monitoring and threat containment
Panoramic dashboard presents ‘first-glance’ view of 11 critical endpoint metrics for each endpoint, providing total security awareness and control
Powerful system management capabilities allow administrators to view and modify endpoint processes, services and installed applications
Supports “push” deployment via Active Directory®, Workgroup and IP addresses and “pull” deployment via group policy or login script
Hierarchical deployment of ESM servers allows local or remote management of non-LAN endpoints
User Assistance manager allows end-users to initiate live-chat sessions with administrators directly from the desktop
Encrypted VNC screen-sharing sessions directly to the end-user’s desktop
Remote assistance feature allows admins to interact directly with users and remote desktop into endpoints if required
Real-time notifications lower emergency response time to emerging threats
Location-aware policies allow granular definition of security configurations for endpoints inside and outside of the VPN
Go Green with integrated power management functionality with Wake-on-LAN enabled systems advance
Drill-down visibility of endpoint metrics including logged-on user and session type, all networking metrics, CPU/RAM/Swapfile usage, Operating system with service pack and version information, installed applications, services and running processes
Minimal system requirements allows installation on non-dedicated Windows PCs or servers
Fast to deploy and easy to manage, CESM is the only endpoint management solution to come with a $5000 virus-free warranty**
*System only
**Comodo's Protection Plan is included with Comodo Endpoint Security and is available for one (1) year from the date of your software registration and installation. Please see Comodo Advanced Endpoint Protection End User Subscriber Agreement (http://www.comodo.com/repository/eula/EULA-CESM-v2013.pdf) for complete details. Comodo Endpoint Security trials exclude Comodo Protection Plan.
FAQs
What protection does Endpoint Security offer?
Comodo Endpoint Security offers 360° protection against internal and external threats by consolidating multiple, cutting edge security technologies in a single, easily installed solution. These include:
- Comodo's powerful antivirus and award-winning firewall solutions
- Comodo's innovative Host Intrusion Prevention System which prohibits untrusted executables from tampering with other processes and files
- Auto-Sandbox™ technology which automatically runs untrusted applications in a contained, isolated environment so they cannot damage the underlying operating system or access user files
- Integrated 'File Reputation' system uses behavior analysis to help determine the trustworthiness of unrecognized files - all without interrupting the end-user
Comodo is so confident that we can protect endpoints against infection that we are the only vendor to offer a $5,000 Limited Virus-Free Warranty 1
How much system resource is consumed on the endpoint?
On idle, the entire 5-in-1 suite only consumes 7.5MB RAM and doesn’t register any CPU usage in Windows Task Manager.
How do I manage endpoints using Comodo Endpoint Security?
Endpoint can be administered via a list, tile or panoramic display interfaces.
Can the management server be run from a virtual server?
Yes.
Can I manage virtual machines?
Yes. ESM can manage full virtualized machines or virtual machines cloned from templates (requires sys prep utility to be run on master template first).
Where do I deploy the endpoint protection server?
The endpoint protection server can be installed on any supported Microsoft Windows operating systems running on a private cloud server, public cloud server or on-premises server.
I manage endpoints in multiple locations, how do I use Comodo ESM?
You can manage all your endpoints from a single endpoint protection server. Alternatively, you can use Comodo ESM 'Dependent Servers' function so that each site has its own endpoint protection server which you can control from an upstream endpoint protection server.
How do I deploy to my endpoints?
Comodo ESM will auto-discover any endpoints in your Active Directory/LDAP containers. Alternatively, you can use the wizards to 'push' the ESM agents to the systems you want managed. You can 'push' deploy to Active Directory OUs, Microsoft workgroups, single IP addresses or an IP address range. You can also download and save the Windows, Mac or Linux management agents to a shared folder, then use login scripts or Group Policy to 'pull' deploy to your systems.
Is alerting/reporting done on a schedule?
No. Comodo's endpoint protection alerting takes place in real-time.
How do I know when something is wrong?
There are several ways that ESM alerts an administrator.
- The endpoints tile icon will change color to indicate an infection has been found, the signature database is out of date, the endpoint is not policy compliant or system resource usage has exceeded pre-defined thresholds.
- The numbers in the information bar's heads-up display will increase.
- Comodo Advanced Endpoint Protection will send you a notification email for any event that you specify.
How are virus database updates received and how are they pushed out?
Virus database updates aren't pushed; instead they are pulled by the endpoint according to the schedule you have set for them. Updates can be received from the Internet or from the ESM server acting as a caching proxy. You can choose to use either (or both) as part of the post-deployment policy configuration. Administrators can also update selected endpoints using the 'Update' button in the administrative interface or on the endpoint's 'Properties' tab.
Can I enable and disable individual components?
Yes. You can choose which components to install (AV/Firewall/Sandbox) during the initial setup or you may re-configure the components at any time thereafter.
Can I configure Advanced Endpoint Protection to use an existing database server?
Yes. Comodo's endpoint protection can use its embedded Microsoft SQL Express 2012 edition or can be configured to use an existing instance of Microsoft SQL 2005 or later (Express, Standard or Enterprise).
Microsoft and Windows are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries.
Apple, Mac and OS X are trademarks of Apple Inc., registered in the U.S. and other countries.
Comodo's endpoint protection is not affiliated with Debian. Debian is a registered trademark owned by Software in the Public Interest, Inc.
Linux® is the registered trademark of Linus Torvalds in the U.S. and other countries.
System Requirements
Endpoint Protection Central Service computer - The host running the Advanced Endpoint Protection Server software
Hardware requirements
- Dual-Core 1.8 GHz processor or better
- 2 GB RAM (4GB recommended)
- 15 GB free disk space if using SQL Express 2008/2012
Software requirements
Operating system
a) Microsoft Windows Server family:
- Windows 2003 Server (SP2 or higher) x86 and x64 editions
- Windows 2003 Small Business Server
- Windows 2003 Small Business Server R2
- Windows 2008 Server (SP2 or higher) x86 and x64 editions
- Windows 2008 Small Business Server
- Windows 2008 Server R2
- Windows 2011 Small Business Server
- Windows 2012 Server
b) Microsoft Windows client family:
- Windows Vista (SP1 or higher) x86 and x64 editions
- Windows 7 x86 and x64 editions
- Windows 8 x86 and x64 editions
Other supporting software (will be installed automatically if not present)
- Microsoft .NET Framework 4.0
- Microsoft ReportViewer 2010 SP1
- Microsoft SQL Server 2012 Express LocalDB
Endpoint Protection Administrative Console computer - The computer that will run the management interface (this computer may also be the Central Service PC)
Hardware requirements
Sufficient to run any of the browsers listed below.
- Microsoft Internet Explorer 10.0 or higher
- Mozilla Firefox 21.0 or higher
- Google Chrome 27.0 or higher
- Comodo Dragon 27.0 or higher
- Opera 12.x or higher
- Safari 5 or higher
- Maxthon Cloud Browser 4.x or higher
Other supporting software (will be installed automatically if not present)
- Microsoft Silverlight 5.1
Display
- Minimum 1024x768 display with windowed browser
- Optional touch capable display interface and operating system
Comodo ESM Endpoints - Managed endpoints that will run Comodo Endpoint Security/Comodo Antivirus for Servers and host the endpoint protection agent
Hardware requirements
- 1.2 GHz processor or better
- 512 MB RAM (1GB recommended)
- 420 MB free hard drive space
Software requirements
Operating system
a) Microsoft Windows client family:
- Windows XP (SP3 or higher) x86
- Windows Vista (SP1 or higher) x86 and x64 editions
- Windows 7 x86 and x64 editions
- Windows 8 x86 and x64 editions
b) Microsoft Windows server family:
- Windows 2003 Server (SP2 or higher) x86 and x64 editions
- Windows 2003 Small Business Server
- Windows 2003 Small Business Server R2
- Windows 2008 Server (SP2 or higher) x86 and x64 editions
- Windows 2008 Small Business Server
- Windows 2008 Server R2
- Windows 2011 Small Business Server
- Windows 2012 Server
c) Apple Mac OS X® client family:
- Mac OS X 10.10
- Mac OS X 10.6.8
d) Debian Linux .deb family:
- Debian x86 and x64 editions
- Ubuntu x86 and x64 editions
Microsoft and Windows are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries.
Apple, Mac and OS X are trademarks of Apple Inc., registered in the U.S. and other countries.
Comodo's endpoint protection is not affiliated with Debian. Debian is a registered trademark owned by Software in the Public Interest, Inc.
Linux® is the registered trademark of Linus Torvalds in the U.S. and other countries.