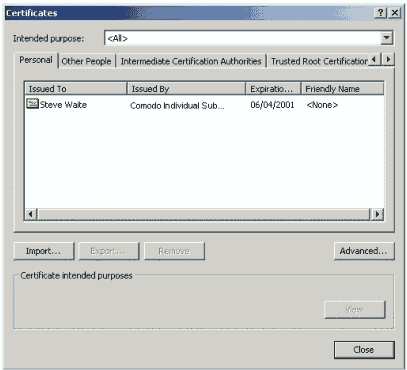
You may view your Digital Certificate store by:
For MS Internet Explorer Users:
1. Open your MS Internet Explorer
2. Click on the Tools menu
3. From the drop down list select Internet Options
4. Click the Content tab
5. Click the Certificates button
If you have enrolled for one (or more), your Digital Certificates will appear within the Personal section. If you have received or downloaded Other People's Digital Certificates, they will appear in the Other People section. You may also view all Intermediary and Root Certificates (belonging to Certification Authorities from this Manager.
To view the specific details of a Certificate, select the Certificate from the boxed list and click 'view'. The Certificate details will then be displayed. These details give general information about the Certificate, who owns it, who issued it, and what it may be used for:
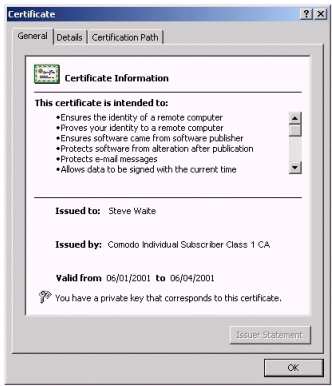
The above Certificate states that the corresponding Private Key is also held. This informs us that this Certificate is being viewed by its owner (as only they have access to the Private Key stated).
To view additional details, click the 'Details' tab. This section details the contents of the Certificate as dictated by the x.509 standard. Clicking on a field will display the specifics of a field:

As discussed previously, it is imperative that a Trusted Certification Authority issue the Digital Certificate in order to prevent fraudulent Certificates being used throughout the PKI. Therefore, we must be able to verify that the Certificate was issued by a CA. This information may be checked in the Certificate Path details:

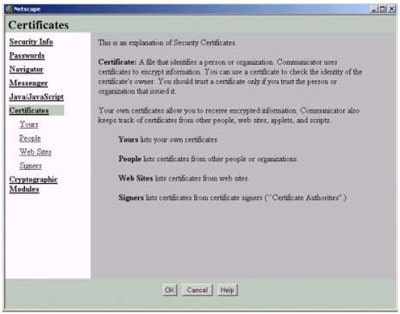
For Netscape Users:
1. Open your Netscape Communicator
2. Click on the Communicator menu
3. From the drop down list select Tools and then select Security Info
4. Click on the Certificates link to view and learn more about each Certificate
type stored by Netscape
What does my Private Key look like?
Private Keys are not easily viewed simply because they need to remain secure. They exist for the most part in an encrypted state within the registry of the Operating System. However, if specified at the time of key pair generation, it is possible to export a Private Key as a data file for backup purposes. Like any cryptographic key, Private Keys are simply long, random numbers.
Preventing unauthorized use of a Private Key
To prevent unauthorized use of a Private Key (especially if the Private Key resides on shared computer) you may specify that access control be applied to the usage of the Private Key. Therefore, when the Private Key is required (for decryption or digital signing), you will be required to confirm use of or will be prompted for the password you have attached to that Private Key.
< Previous