Cybersecurity Webinar
Advanced Endpoint Protection
File Rating Integration with Microsoft, Comodo, File Lookup Server and Valkyrie
September 15, 2020 11:00 AM EST
LEARN HOW TO INTEGRATE COMODO CYBERSECURITY TO YOUR EXISTING ENDPOINTS TO STOP ACTIVE BREACHS
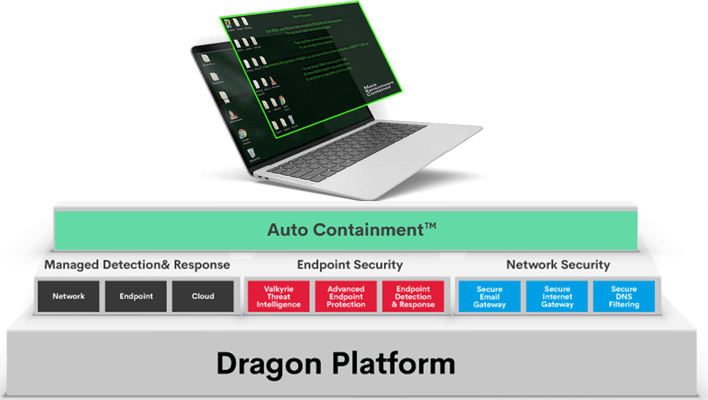
Join us for this important and informative webinar as we provide you the best practices to integrate your existing endpoints onto the Comodo Cybersecurity Dragon Platform to enable Zero Trust Architecture and patented Auto Containment technology.
IN THIS WEBINAR WE WILL BE TALKING ABOUT BELOW TOPICS;
- The File itself cannot be dangerous until executed. File Rating capability will help preventing threats.
- CCS always calculates the rating for every executable and script once it is executed.
- The file rating can be: Trusted, Malicious, Unrecognized (Unknown)
- The rating sources by priority
- If no one rating provider returned Trusted or Malicious, the file will be submitted to Valkyrie for Analysis and reported to the EM portal.
Recorded Sep, 15 2020 | 60 Minutes
Presented by
Zeynep Yıldırım, Senior Product Manager
Register Now
Complete this form to register for this webinar.