Comodo PKI for IoT Security
Utilizing more than 20 years of experience with PKI and SSL, Comodo provides organisations with trusted, mutual-authentication solutions for all Internet of Things (IoT) devices and networks.
In today’s connected world, mutual-authentication of devices and networks is critical to maintaining a secure and healthy ecosystem. Whether you are a device manufacturer, service provider or standards body, privacy and security of your devices, networks and standards must be protected. Too many devices are getting connected to networks around the world with weak or zero security pre-installed. Without proper security, you are exposing your customers and your organization to rogue, infected and/or malicious devices.
It is crucial for a relationship to be established between the hardware and software of an IoT device. Neither can go it alone and by using PKI technology, this relationship can be "connected" to enable a truly secure out of the box device.
By utilizing more than 20 years of experience with PKI and SSL, Comodo provides organizations with trusted, mutual-authentication solutions for all IoT devices and networks. Using x.509 PKI certificates and custom hybrid SSL certificates, Comodo’s high-availability, batch-issuance system allows for administrators to easily enroll, download and decrypt certificate batches quickly and efficiently.
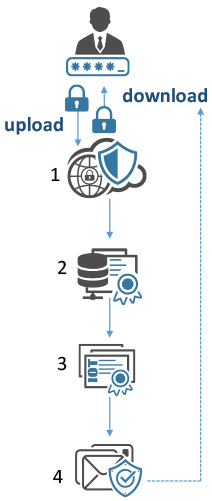
How it works...
- Administrator logs into Comodo Certificate Manager Portal and submits batch enrollment
- Comodo signing servers sign the Batch request
- Signed certificates are placed into an encryption file
- Administrator is notified via an email when batch file is ready for download
- Administrator logs into portal and downloads encrypted file.
- Using provided decryption tools, the administrator decrypts the file.
Features of Comodo IoT PKI
- Algorithm Support for ECC 256/384 & RSA 2048 & 3072
- FISMA Certified Tier-5 Datacenter (Coming Soon!)
- 24X7 service availability with "Follow the sun support"
- Use Comodo’s secure infrastructure versus the hassle and expense of managing your own internal PKI service
- Leverage of 50+ years of experienced PKI personnel
- An experienced and trusted security services provider
Are you responsible for setting up a new ecosystem for connected IoT devices?
This could pose quite a challenge to your organization. Having the right expertise for the right industry requires years of on-hands experience. Let Comodo assist you with developing these critical documents that will align the needs of the organization with the proper security policies and procedures required for your industry and any applicable standards.
Industry Memberships

Comodo Ecosystem Set-Up
- Creation of Certificate Profile(s)
- Drafting of Certificate Policy
- Drafting of Certificate Practices Statement
- HSM Provisioning and Management
Can you issue your own PKI certificates but want to do so from a trusted 3rd CA hierarchy?
- Comodo can assist with CA Signing and Hosting services.
CA Signing and Hosting Service
- Root CA Signing
- Subordinate CA Signing
- Securely hosted and stored in a tier 5 datacenter using Hardware Security Module (HSM) technology
Contact Us
iotpki@comodo.com
+1-844-260-3374
