Dragon for Enterprises | Endpoint Protection Platform
Complete endpoint protection with extensive threat hunting and expanded visibility – Dragon Enterprise
Dragon Enterprise - EPP Security Benefits
While unknown files are in containment, the files are immediately analyzed in the cloud by Comodo’s Valkyrie Verdicting Engine and Threat Intelligence without interrupting the end user.

100% Trusted Verdict of Every Unknown File

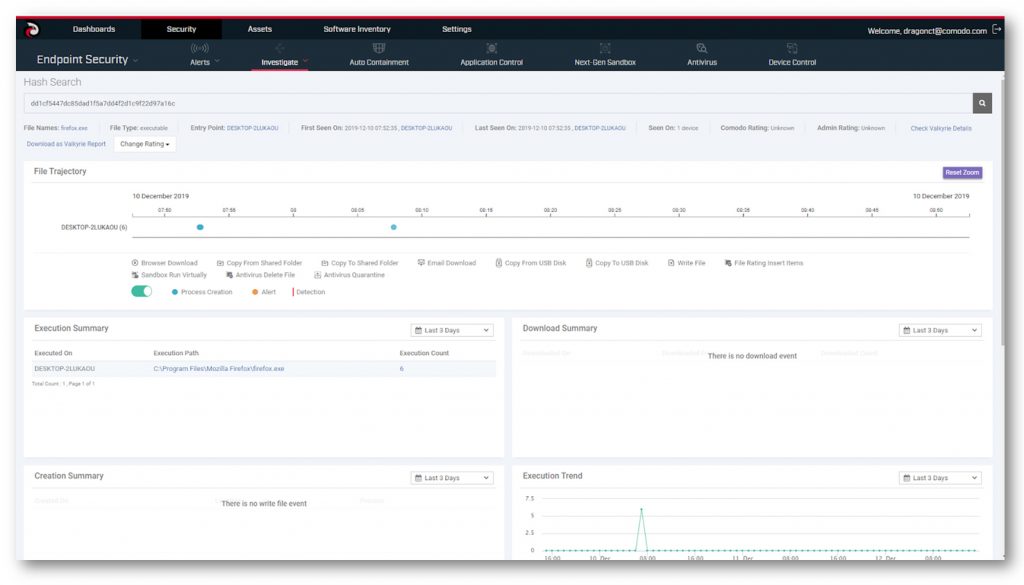
Clear Visualization of Event Timelines

Lightweight Agent with Cloud Delivered Updates

Visual Incident Investigations and Activity Alerting
Enterprise-Grade Security Against Ransomware, Data Breaches, & Malware – Dragon Enterprise
Dragon Enterprise gives the complete and actionable visibility into endpoints paired with powerful zero trust architecture.
- Security Architecture
- Threat Visualization
- Threat Database

- Protect endpoints against 100% of unknown threats without impacting user productivity.
- Combination of machine learning and human expert analysis gives your verdict in 45 seconds.
- Once Advanced Endpoint Protection is deployed it won’t heavily impact endpoint performance.
- Allow unknown files to safely run on endpoints, without write access to the critical components.
- Virtualize all unknown files immediately in Containment when executed on an endpoint.
- End users enjoy seamless productivity, with the ability to run any unknown file, even while the file is in analysis.

- 95% of unknown files return a verdict under 45 seconds! 5% of unknown files go to security specialists with 4 hour sla!
- Security specialists are on call to apply expert analysis of more sophisticated threats and return a verdict in a maximum of 4 hours.
- File Verdicts are updated globally in real-time for all AEP customers by the Valkyrie verdicting engine.
WHY CHOOSE OUR
DRAGON ENTERPRISE | ENDPOINT PROTECTION PLATFORM
Contain 100% of known and unknown threats instantly
Monitor important operating system activities to watch for intrusions
Automatically detect, cleanse and quarantine suspicious files
Protect against malware that have no files to execute
Protect against inbound threats and outbound threats
Statically and dynamically analyze unknown threats in the cloud
Check the file reputation against Comodo’s whitelist and blacklist
Signatures updated automatically without interruption
Monitor behaviors of all processes to identify harmful actions
24 hr expert analysis of more sophisticated threats
Analyst Recognition – Dragon Enterprise
We’ve won consecutively across many verticals with our premier technology.
Innovation happens only when this type of dedication to cybersecurity reaches the many.
![]()
![]()
![]()
![]()
![]()
Dragon Platform, formerly Comodo ONE, selected as SC Media 2018 Trust Award Finalist for Best Managed Security Service
Comodo Threat Intelligence Named Best in Cloud File Analysis in 2019 Cybersecurity Excellence Awards
Comodo Threat Intelligence Named 2019 Finalist for Trust Award in Best Threat Intelligence Technology by SCAwards
Internet Gateway
Pair Endpoint Detection & Response with Advanced Endpoint Protection for increased endpoint visibility to detect threats and investigate and respond to security incidents.
LEARN MOREDetection & Response
Pair Managed Detection & Response with Advanced Endpoint Protection to outsource the management of your networks and endpoints to Comodo to prevent breaches.
Email Gateway
Pair Valkyrie Threat Intelligence with Advanced Endpoint Protection for even more visibility into the dark and deep web using over 150 intelligence feeds to notify your admins if domains/IPs are under risk of any phishing, virus, spam and risks on your domains.
LEARN MORE