What is EDR?
EDR (Endpoint Detection and Response) is a cyber security software that helps protect computers and networks from cyber threats. EDR tools work by monitoring data traffic and identifying suspicious activity continuously. They can then take action to block or quarantine potential threats. EDR tools are an essential factor in a comprehensive security strategy. They can help organizations detect and respond to cyber threats quickly and effectively. EDR tools can also be used to investigate incidents after they occur.
How Does EDR Work?
EDR systems are designed to complement traditional security solutions such as antivirus and firewalls. While these solutions effectively protect against known threats, they cannot always detect or respond to new or unknown threats. EDR provides an additional layer of protection by constantly monitoring devices for suspicious activity and reacting quickly to potential threats.
- An agent is installed on each endpoint.
- A central management console.
- A cloud-based analytics service.
The agent monitors activity on the endpoint and sends information back to the console, where the analytics service can analyze it.
Key EDR Functions
The exact capabilities of an EDR solution will vary depending on the vendor, but most solutions offer similar features, such as:
- Threat detection: EDR solutions use multiple techniques to detect malicious or suspicious activity on an endpoint. This includes behavioral analytics, heuristics, and machine learning algorithms.
- Threat response: Once a threat has been detected, EDR solutions can take action to block or contain it. This may involve quarantining the infected files, isolating the device from the network, or deleting malicious files.
- Reporting and alerts: EDR solutions can generate reports on detected threats and send alerts when certain thresholds are met. This helps administrators stay informed of potential threats and quickly mitigate any damage.
Things to consider on choosing EDR Solution
When evaluating an EDR solution, you should consider its ability to effectively detect and respond to threats and its impact on performance and false positives. The ideal solution will have a high detection rate for known and unknown threats while minimizing false positives and maintaining good performance.
The benefits of EDR
EDR, or endpoint detection and response, is a rapidly growing field in cybersecurity. EDR tools are designed to detect and respond to threats at the endpoint level, providing a last line of defense against sophisticated attacks.
There are many benefits of using EDR tools, including:
- Increased visibility into endpoint activity: EDR tools provide detailed visibility into what happens at any given time. It includes processes, files, registry keys, and network connections. This data is used to identify and investigate suspicious activity quickly.
- Enhanced detection capabilities: EDR tools use various techniques to detect malicious activity, including behavioral analysis and machine learning. It means that they can often detect threats that traditional antivirus solutions miss.
- Faster response times: Because EDR tools provide real-time visibility into endpoint activity, they can help security teams respond quickly to incidents. It can minimize the damage caused by attacks and reduce recovery time.
- Improved forensics: EDR tools collect extensive data about endpoint activity that can be used for forensics. This data can help investigations identify the root cause of an incident and determine which systems were affected.
- Reduced false positives: EDR tools typically generate fewer false positives than other security solutions, such as intrusion detection systems (IDS). It means that security teams can focus on investigating actual incidents instead of wasting time chasing false alarms.
How to implement EDR?
Endpoint detection and response (EDR) is a critical security measure for businesses of all sizes.
Here's how to implement EDR in your organization:
- Define your goals. What are you hoping to achieve with EDR? Do you want to detect threats or also respond to them? Be clear about your objectives before proceeding.
- Choose the right platform. Many EDR platforms are on the market, so research to find the one that best fits your needs. Consider features like ease of use, integration with other security systems, and cost.
- Deploy the system. Once you have selected a platform, follow the instructions for deploying it in your environment. It typically involves installing software agents on endpoint devices.
- Configure detection rules. For EDR to be effective, you must configure detection rules that identify suspicious activity. These rules can be based on file type, process name, network traffic, etc.
- Review alerts and act. Once EDR is up and running, it alerts when suspicious activity is detected. Review these alerts carefully and take appropriate action, which may include investigating the source of the threat and taking steps to neutralize it.
Get Real-Time Endpoint Detection And Response (EDR) Forensics
 Learn from every attack encounter.
Learn from every attack encounter. Mature your environment.
Mature your environment. Benefit your organization by getting the full picture.
Benefit your organization by getting the full picture. Continuously improve your security posture by staying 2 steps ahead of your attackers!
Continuously improve your security posture by staying 2 steps ahead of your attackers!
Reap The Value Of Endpoint Detection And Response In A ZeroDwell Time World
ZeroDwell technology disrupts the industry focus on detection-first approaches to cybersecurity. Detection as the first line of defense is clearly not working: breaches keep coming at all of us, and the threat landscape becomes more and more malicious.
Nonetheless, EDR visibility, detection and remediation are always needed to harden environments, patch vulnerabilities, deepen threat hunting capacities, and sync with human-led global intelligence and re-engineered attacker threat paths to stay ahead of threats and continue to innovate.
With ZeroDwell, Xcitium pre-empts detection and response maneuvers with instant virtualization of Unknowns as they enter your endpoints. Detection is not protection, but ZeroDwell Containment changes all that with its proven, powerful zero trust virtualization. Once protected with patented attack isolation, effective EDR begins with enhanced awareness, visibility and remediation of environment vulnerabilities.
With your security team no longer burdened by excessive alert fatigue, you can be empowered by Xcitium's superhuman x-ray vision and management of the whole enterprise. Xcitium Endpoint Detection Response (EDR) visibility and forensics start with ZeroDwell Containment virtualization.

Attack vector data combined with file trajectory and process hierarchy data points and displayed on your dashboard to streamline patching and vulnerability repairs. Process-based events are shown in a tree-view structure to help your analysts better understand process behavior. Device trajectory details are also provided with separate displays to drill down into devices for insight when investigating attack vectors.
Patch Your Vulnerabilities Keep your endpoints up to date using Endpoint Detection And Response
Patching protects against zero-day web threats without hindering employee productivity. Analyze 100% of unknown fileless threats with Xcitium's intelligent file analysis engine. Apply our recommended security policies, created via meticulous examination of threat behavior analytics.
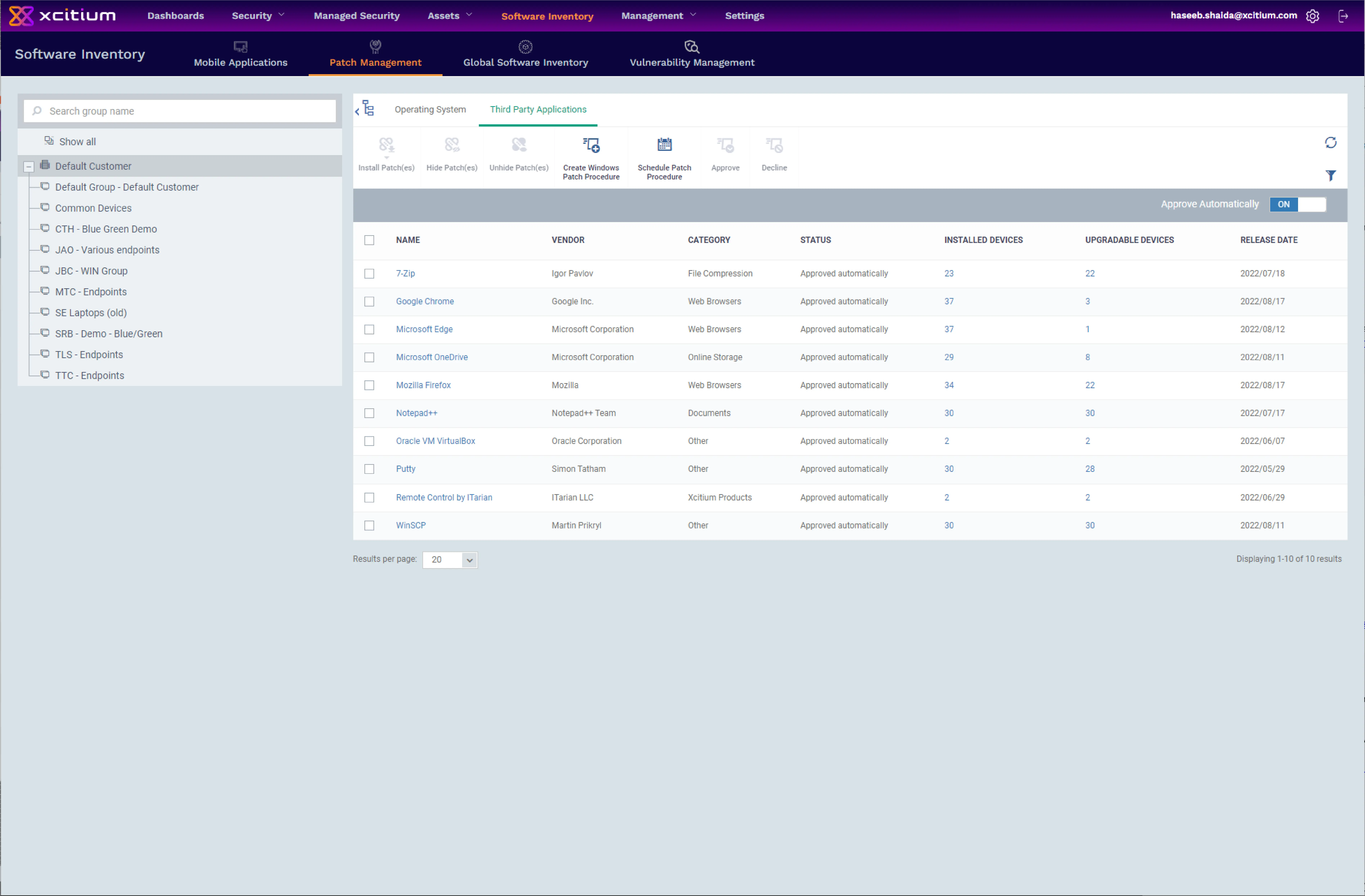
Endpoint Detection And Response Includes Full Detection Forecast Analysis
Xcitium Advanced Endpoint Detection Response (EDR) tailors group policy to your customized requirements, including endpoint-specific policies for enhanced security. No hardware is needed! Automatically updates signatures and checks processes executed in your environment with continuous monitoring. Dramatically streamlines follow-up efforts for your IT departments and forensic teams.

FAQ section
A: EDR is beneficial for organizations of all sizes and across various industries. It is particularly valuable for businesses with a large number of endpoint devices and those dealing with sensitive data. Customizable EDR solutions cater to the specific needs of different organizations.
A: Traditional antivirus software primarily focuses on detecting and blocking known malware. EDR, on the other hand, offers broader and more advanced capabilities. It monitors and analyzes endpoint behavior, detects unknown and fileless threats, and provides proactive threat hunting and response features.
A: EDR doesn't replace but mostly combined forces along with other security solutions. It works alongside traditional antivirus software, firewalls, and other security measures to provide a comprehensive defense strategy. EDR adds an additional layer of protection by focusing on endpoint activities.
A: While EDR is highly effective in detecting and responding to many cyber threats, it cannot guarantee complete prevention. It significantly reduces the risk of successful attacks but should be used in conjunction with other security measures and best practices to ensure comprehensive protection.
A: Most of the reputable vendors offer easier user interfaces and thorough documentation to implement and manage EDR. Although it's worthy to mention the requirement of experts are somewhat needed to make configuration and monitoring as seamless as possible.
A: The security teams usually needed EDR to preempt the threats and adopt remediation measures by getting insight into endpoint visibility, real-time alerts, and comprehensive intelligence on threat methods.
A: EDR solutions primarily focus on monitoring endpoint activities for security purposes. To address privacy concerns, organizations should clearly define and communicate their data collection and usage policies. Implementing proper access controls and anonymizing sensitive data can help protect privacy while leveraging EDR's benefits.