Do you know that more than 67 percent of firms suffer from cyber-attacks? And 80 percent of these attacks were New ZERO-Day Attacks.
There is a need to stop these rising threats by installing Endpoint Detection Response software at multiple endpoints. And when it comes to one of the best EDR solutions, the name Malwarebytes appears on the surface.
Do you want to know what Malwarebytes is? And how it's making an organization's network more secure than before? Continue reading and get a complete picture in mind.
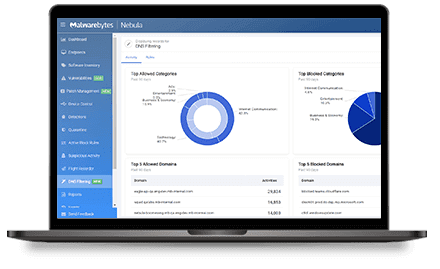
What is EDR Malwarebytes - Definition
It is an Endpoint Detection and Response Software by Malwarebytes. This leading cyber security boosts data and network safety by:
- Detecting suspicious activity on all endpoint security levels
- Investigating known and unknown threats
- Isolating attacks at multiple layers
- Stopping attacks before they cause any widespread harm
- Remediating damage with its unique 72-hour ransomware rollback for Windows
In simple words, this EDR solution continuously monitors all endpoints connecting to your company's network security.
What is EDR Malwarebytes - Benefits
Here are some benefits that make this Endpoint Detection and Response Solution reasonably practical and helpful for organizations.
- Non-Disruptive and Super Compatible
Perhaps your organization already has Microsoft Defender installed in the network, but still, you need to secure your endpoint against the advanced threat. In that case, you can rely on the Malwarebytes endpoint protection solution.
The best thing about this software is that it's non-disruptive. In addition, it's compatible with other EDRs in the market. When it comes to protecting endpoints against hidden threats of trojans, rootkits, and backdoors, it's hard to find any perfect match like Malwarebytes.
- Detection of Known and Unknown Threats
It's time to be proactive with your cyber security solutions. Most antivirus is designed to deal with known threats.
But what about the unknown?
How are you going to secure your organization against unknown threats?
Sweat not.
EDR Malwarebytes endpoint protection is super effective. This threat detection system relies on unique Anomaly Detection machine learning. Thereby, it can secure endpoints against both known and unknown threats.
- Accuracy at its Best
Another benefit of using this solution is to enjoy a high level of accuracy. With other EDRs, High false positive is a big issue, but not anymore. Your organization can save its resources through low false positives. In addition, the solution can detect zero-day threats.
- Malwarebytes Vs. EDR
You'll come across many as soon as you explore the different solutions for protecting your organization's endpoint. But Malwarebytes endpoint protection is far different and better than others. You may wonder how? Here are some main differences between other Endpoint detection and response solution and one provided by Malwarebytes
- Easy to Scale
Organizations can enjoy a low cost of Ownership with Malwarebytes. Since you get a cloud-native solution, it's easy to meet future endpoint security requirements with this software. However, you can't scale up your endpoint security with other EDRs, as most do not offer cloud-native systems.
- Easy to Integrate
In the future, if an organization has multiple endpoints, a cyber threat intelligence system from Malware will make a big difference. It is super easy to integrate the API of Malwarebytes with SOAR, SIEM, ITSM, etc. Enterprises planning to automate the complete threat detection and remediation process can make the most of Malwarebytes EDR. Other EDRs are more complex to integrate, though. Since they are challenging to deploy and manage, the organization would prefer Malwarebytes EDR due to its simple deployment and management.
If you need a better alternative to Malwarebytes EDR, it's available in the form of Xcitium EDR. It won't burden your security team with excessive alerts. Thanks to Xcitium's superhuman x-ray vision and management, you can drop down false positive rates. With Xcitium Endpoint Detection Response (EDR) visibility and forensics, your security team can focus more on real threats and less on fake ones. It boosts their productivity and saves organizational resources.
- Multiple Layers of Isolation
One unique feature of EDR by Malwarebytes is its multiple layers of Isolation. Other EDRs don't offer this kind of security solution.
Let's suppose you detect a threat via Malwarebytes EDR. Now you can isolate the network security, desktop, and process. This Isolation ensures that Malware won't spread any further in the network security and won't cause any damage to users, data, and the system as a whole.
- Lightweight Agent
What makes EDR Malwarebytes endpoint protection better than every other Endpoint Detection and Response solution in the market is that this powerful software is a lightweight agent.
What does it mean?
It runs in the background as a threat intelligence officer without impacting overall system performance. It requires your network to run three processes in the background- only three while other EDR solutions rely on several processes to ensure your system security.
Wrap up - What is EDR Malwarebytes
If your organization wants to get a powerful EDR that can help you protect your endpoints against known and unknown threats, it's always suggested to rely on EDR Malwarebytes. It is easy to integrate, deploy, and manage. In addition, you can add this EDR into your system without removing other EDRs, thanks to MB EDR's excellent compatibility feature.
Do you need another cloud-based powerful EDR for your Windows network? Then, why don't you consider Xcitium EDR? It offers the most effective endpoint security with low maintenance and better ROI.