What does a Firewall do? - Network Security Firewall
Step by step process flow of how firewalls work to protect your personal computer and private network from malicious mischief.
Step by step process flow of how firewalls work to protect your personal computer and private network from malicious mischief.
At their most basic, firewalls work like a filter between your computer/network and the Internet. You can program what you want to get out and what you want to get in. Everything else is not allowed. There are several different methods firewalls use to filter out information, and some are used in combination. These methods work at different layers of a network security firewall, which determines how specific the filtering options can be.
Firewalls can be used in a number of ways to add security to your home or business.
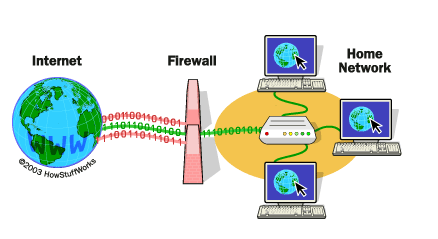
Computer Network Firewall protection
Comodo Firewall Security uses the latter way to prevent malware from installing on your computer. This free firewall software, from a leading global security solutions provider and certification authority, uses the patent-pending "Clean PC Mode" to prohibit any applications from being installed on your computer unless it meets one of two criteria. Those criteria are a) the user gives permission for the installation and b) the application is on an extensive list of approved applications provided by Comodo. With this feature, you don't have to worry about unauthorized programs installed on your computer without your knowledge.
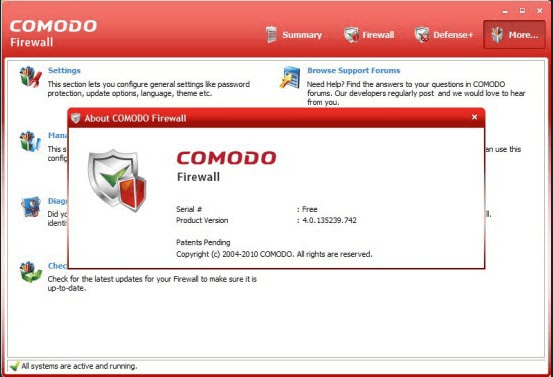
This software is highly customizable so that you can adjust it to suit your specific needs.
Comodo Internet Security Suite combines the award-winning Comodo firewall security with a powerful antivirus to offer a multilayered approach to protecting millions of computers around the world for free.
Comodo Complete Antivirus and Firewall $29.99/year.
Got more than 1 PC? Get 3 Licenses for $39.99